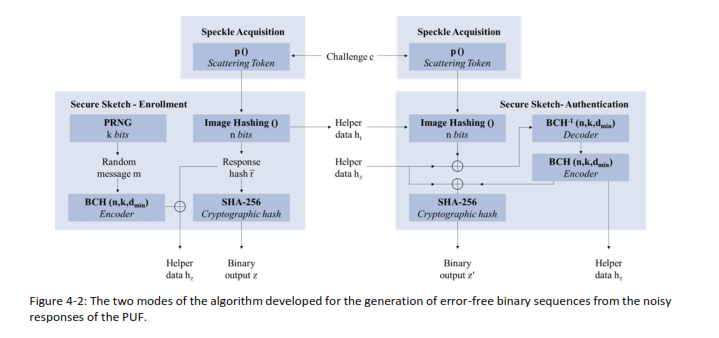
We’re excited to share a core component of our work in the Allegro Project – the Post-processing Algorithm that transforms raw optical speckle patterns into cryptographically secure binary sequences, without storing any raw experimental data. This is a major step towards on-demand, privacy-preserving physical unclonable functions (PUFs).
🔍 How it works:
Our method builds on the concept of a fuzzy extractor and comprises three essential steps:
1️⃣ Compressive Sensing-based Image Hashing
We convert experimental speckle patterns into 511-bit binary sequences that satisfy the three core PUF properties: uniqueness, reliability, and unpredictability.
This is done via:
📌 Image alignment
📌 Feature extraction (e.g., prominent geometric features)
📌 Binarization via quantized Fourier-transformed white-noise-modulated speckles
🧠 In simple terms:
We apply a random Bernoulli modulation, followed by a Fourier transform, and use a pseudorandom sampling and quantization function to generate highly secure binary keys on the fly.
🧾 Represented as:
r = 𝒬 {𝑆 [ℱ(B ∘ 𝑟)]}
Where each part of the equation plays a role in aligning, modulating, transforming, and sampling the speckle pattern to yield the final binary sequence.
🔐 This enables secure, stateless key generation, perfect for resource-constrained edge devices and zero-trust hardware authentication environments.
💡 The approach is fully in line with cryptographic requirements, leveraging insights from works like [Arm11, Arm16, Sha12], and combining them with robust signal processing techniques [Har88, Can08, Ala12, Nai09].
🔗 Stay tuned as we integrate this into next-gen PUF-enabled SmartNICs and DPUs for secure edge intelligence.
#AllegroProject #PUF #Security #EdgeComputing #DPUs #CompressiveSensing #Speckle #FuzzyExtractor #SmartNIC #HardwareSecurity #Cryptography #AIoT #TrustworthyComputing